Should Your Site Block VPNs and Proxies?
 Virtual Private Networks (VPNs) and other types of proxies are an increasingly common way to surf the web.
Virtual Private Networks (VPNs) and other types of proxies are an increasingly common way to surf the web.
To end users, these services provide a great deal of benefit. They increase anonymity, improve security and can help avoid throttling by ISPs. However, in recent years, much of the focus on VPNs and proxies have been on their ability to circumvent geographic boundaries, such as accessing Netflix when outside the United States.
This anonymity and lack of geographic boundaries poses a lot of challenges for webmasters. For those providing content intended for only one nation, VPNs are a simple means of circumventing basic geoblocking technology. This is why sites like Hulu actively seeks to block VPN users.
But it isn’t just Hulu that’s interested in blocking VPNs and proxies. The anonymity has made VPNs popular with spammers, scrapers, hackers and others that wish to do your site harm. That is partly why Escapist Magazine, along with many other sites, have moved to block traffic from suspected VPNs and VPN-like connections.
So is it time for you do the same? The answer is probably not, but this is definitely a trend that webmasters should be watching very carefully over the next few years.
What is a VPN (or Proxy)?
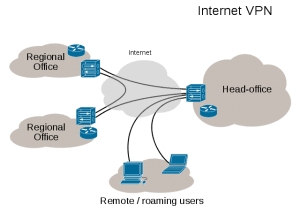 To understand the problem, we have to look at what a VPN is and how it works. However, the easiest way to do that is to start by looking at proxies and understand the principle behind them.
To understand the problem, we have to look at what a VPN is and how it works. However, the easiest way to do that is to start by looking at proxies and understand the principle behind them.
If you don’t use a VPN or a proxy, whenever you visit a website or a service online, that service has your Internet Protocol (IP) address. That IP address is how the server communicates with you, sending you the data that you requested to it.
A proxy, however, is simply a middle man. Rather than communicating directly with a website or service, you instead connect with the proxy, which then passes along your request to the end destination. That server then responds to the proxy, which passes along the replies to you.
While this process is less efficient than a direct connection, it means that your IP address is never passed along to the server. All that the end server sees is the IP address of the proxy, which can be anywhere in the world
That’s useful because, while IP addresses are not unique to an individual, they do carry a lot of useful information such as an approximate location, what ISP you’re using and, if combined with other data, can be used to build a profile of your surfing habits. Proxies, however, are shared by many people and can be anywhere in the world.
VPNs are basically proxies but with one key difference, the traffic from your computer the host server (or VPN server) is encrypted. This means that no one between you and your host server can see the details of what you’re doing. This includes your ISP, anyone on your local wifi or even governments if they aren’t able to get access to the VPN logs.
VPNs have become very popular for security reasons. Many companies require off site employees and contractors to dial into the company’s local network using a VPN to ensure security. VPNs are also highly encouraged at open wifi hotspots where, without one, traffic might be sniffed for crucial information.
However, VPNs have also become popular for less-than-scrupulous reasons. Those who routinely pirate content often use VPNs to avoid being sued or receiving warnings from their ISP. Hackers, spammers and other bad actors online also often use VPNs to hide their source and make themselves more difficult to catch and prosecute.
And it’s those bad actors that put webmasters in a difficult spot when it comes to VPNs and why more and more are choosing to block them at the border.
The Case for Blocking VPNs
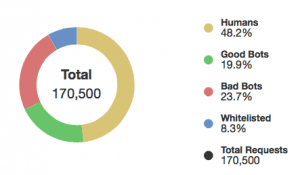 If you run a website, odds are that a sizable percentage of the traffic you see doesn’t come from human visitors, but from automated bots of one sort or another.
If you run a website, odds are that a sizable percentage of the traffic you see doesn’t come from human visitors, but from automated bots of one sort or another.
According to Distil, the company that provides protection for Plagiarism Today, only 48.2% of all requests to this server are human. 19.9% are “good” bots, such as search engines and social networks and 23.7% are bad bots, such as spammers, scrapers, etc. The remainder is traffic I specifically whitelisted for one reason or another.
This unwanted traffic brings with it very serious problems including spamming, content scraping and hacking attempts. These attempts, disproportionately either come from VPNs and proxies or from data centers that host VPN servers.
This is because most commercial VPNs don’t operate in the same IP ranges that consumer connections do. Since they are typically hosted in large data centers, they share similar IP addresses with other servers, not other end users.
As “Kross”, the server administrator for Escapist, put it:
There is extremely little legitimate website traffic from data centers (all the major crawlers that send traffic like google/facebook/etc have their own IP allocations), and what little there is very rarely view ads that pay for their resource usage. And for the remaining few that do need proxies for actual connectivity reasons, I am always happy to work out a solution.
Most webmasters, however, haven’t taken this step. While media-intensive and ad-dependant sites like Escapist certainly can see real harm proxies and VPNs, most don’t. The bad bots, whether spammers, scrapers or hackers, don’t have a broad enough impact on a site to warrant blocking proxies, data centers or any other large chunk of the web.
But as VPN and proxy usage continues to rise, the question is going to get asked: When and if should you start blocking VPN users?
Should Your Block VPNs?
 For most websites, the answer to the question “Should I block VPNs?” is a solid no. It just isn’t worth it.
For most websites, the answer to the question “Should I block VPNs?” is a solid no. It just isn’t worth it.
The actual harm to your site caused by VPNs is minimal and services like Distil can Incpasula can help mitigate bots and bad actors without blocking large sections of the web. (Note: CloudFlare also provides this service though I don’t recommend them due to their standing on copyright issues.)
That being said, this is still a question every webmaster has to weigh for themselves. Escapist reached the decision because they were wasting a great deal of traffic on visitors from data centers and decided to block them. VPN users, it appears, were largely innocent bystanders.
Still, if you aren’t seeing significant harm from VPN users (and you likely aren’t) and you don’t have some reason to strictly enforce geoblocking, you probably have little need to block VPNs and proxies.
In the meantime, there are other defense mechanisms, including those listed above and on-server solutions such as BulletProof Security and All in One WP Security & Firewall, which can help limit the activity of bad bots.
Intermediate steps such as those are, for most sites, much more prudent.
However, if you’re still convinced you need to block VPNs, doing so is not a simple matter.
How to Block VPNs Visiting Your Site
![]() Before you begin your effort to block VPN access to your site, there are three things you need to consider.
Before you begin your effort to block VPN access to your site, there are three things you need to consider.
- It is Very Difficult: Blocking VPNs and proxies is not as simple as it seems if you want to do it well. VPNs in particular are often well-hidden and they are constantly changing IP addresses.
- It Will Never be Complete: Even the best blocking system will miss some VPNs. If a major company like Hulu can’t catch all VPNs, neither can any service you implement.
- You Will Block Legitimate Users: As discussed above, just as there are unethical reasons to use a VPN, there are practical ones too. By blocking VPNs, you block the security conscious at the same time you block spammers, meaning you will lose at least some legitimate visitors.
If blocking VPNs is still worth it, the easiest, albeit most expensive, way is to turn to third party software, such as those provided by BlockedScript.
If you’re more interested in just blocking proxies, you can make changes to your server to block most proxies. This works best against open proxies though there are other edits to block “tough” proxies. Still, these methods are going to miss VPNs, especially those that are trying to be hidden.
There are also WordPress plugins that can help automatically implement some of these strategies.
All in all though, any strategy to block VPN is either going to be time consuming, relatively expensive or only partially effective.
It’s yet another reason why such a strategy isn’t likely a good move at this time.
Bottom Line
In the end, if you’re a webmaster, unless you have some specific problem with VPNs or proxies, there’s no reason to block them at this time. There are other means of mitigation against bad actors that don’t involve blocking many legitimate users and are much easier/cost effective to implement.
That being said, it is an issue and a debate that webmasters should watch. As VPNs and proxies continue to grow in their use, the question is whether the uptake will be mostly by legitimate users or those seeking to harm sites. So far, it seems to be the former, but with more and more VPNs advertising themselves directly to pirate-friendly and hacking crowds, that could change.
Also, as time moves forward, services and tools to block VPN will get cheaper. They might not get more effective because there will always be new IP addresses brought online, but they will become cheaper and easier to use.
It’s possible, though not necessarily likely, that there will come a tipping point where VPNs are abused enough and VPN blocking is easy enough that it’s worthwhile to do. That time isn’t now, for most sites, but it’s still a possibility in the future.
Want to Reuse or Republish this Content?
If you want to feature this article in your site, classroom or elsewhere, just let us know! We usually grant permission within 24 hours.
