Plagiarism Today Moves to HTTPS (And How You Can Too)
 Note: This is not a typical Plagiarism Today post in that it’s not about copyright or originality issues, instead, it’s about a website development issue that may impact many members of the site’s audience. Still, if you aren’t interested in the nuances of moving a site to HTTPS (HTTP Secure), feel free to skip this post, normal content to resume Tuesday.)
Note: This is not a typical Plagiarism Today post in that it’s not about copyright or originality issues, instead, it’s about a website development issue that may impact many members of the site’s audience. Still, if you aren’t interested in the nuances of moving a site to HTTPS (HTTP Secure), feel free to skip this post, normal content to resume Tuesday.)
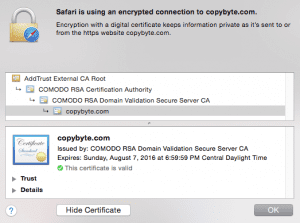
If you haven’t visited either PlagiarismToday.com or CopyByte.com in the past few days, you might spot something new: A green lock. Both of the domains have been moved to HTTPS, meaning that they are delivered over a secure connection, similar to the one that one often looks for when sharing payment or personal details online.
The move had been planned and sought after for quite some time but when, earlier this month, Google announced it was considering SSL as a ranking factor in search results, I decided it was time to move up the plans.
Most likely, other websites are going to be looking at making a similar move. So, I want to take some time to explain both why this move is important, how to do it yourself and what are some of the common challenges you will likely find along the way.
Why HTTPS Is Important
 SSL stands for Secure Socket Layers (Note: Though Transport Layer Security, or TLS, is the most common protocol, most still refer to it as SSL colloquially) and basically means that the data being transferred between a site, such as Plagiarism Today, and your computer is encrypted. As stated by Ilya Grigori and Pierre Far of Google in a recent talk, this is important for three reasons.
SSL stands for Secure Socket Layers (Note: Though Transport Layer Security, or TLS, is the most common protocol, most still refer to it as SSL colloquially) and basically means that the data being transferred between a site, such as Plagiarism Today, and your computer is encrypted. As stated by Ilya Grigori and Pierre Far of Google in a recent talk, this is important for three reasons.
- Authentication: When you see that a site is labeled as secure, you can be (reasonably) certain that you are visiting that site and not a third party’s site posing as it.
- Data Integrity: Ensures that the data is not manipulated (either direct) in transit and that both sides see exactly what the other sent.
- Obfusication: Since the data going between the two computers is encrypted, anyone looking at the information as it travels will not be able to glean anything of value. This includes everything from ISP-level snooping to simple snooping on an open wifi.
Historically, most sites like Plagiarism Today have been transmitted “in the clear”, meaning that the data is unencrypted. Encryption wasn’t seen as necessary for sites that didn’t transmit personal, financial or other sensitive data. The danger of spoofing, or another site pretending to be Plagiarism Today, was considered low and the harm that could be done was seen as minor.
But in 2014 the threats are different. Snooping isn’t just about a person sitting on an open wifi hoping to grab a few unencrypted credit card numbers. Snooping takes place on an ISP, national and even global level. It’s not just about identity theft and credit card fraud (though those are still major threats), it’s also about general privacy.
The fact you read a few articles on Plagiarism Today might not reveal much about you. But combine that with other information, often transmitted in the clear online, an observer could build an effective profile for a variety of means. This could include anyone from a lone user sitting on an open wifi to a government trying to profile your habits.
While SSL is primarily thought of as a security tool, it’s also a privacy tool. While I don’t see Plagiarism Today as a likely target for privacy issues, the more of the Web that’s encrypted, the better privacy is and, by flipping the switch, I’m doing my small part to make the Web a bit more private (while also, hopefully, gaining a small boost from Google).
Move Your Site to SSL
Setting up a site to work through SSL involves the same basic series of steps.
- Purchase an SSL Certificate: You have to purchase an SSL certificate from a trusted issuer.
- Apply the Certificate to Your Server: Install the certificate on your server, usually through your site’s control panel.
- Redirect Traffic to httpss: Then direct all visitors the httpss, or secure version of your site.
However, as I found, those steps are easier said than done, at least in some cases.
Though Plagiarism Today and CopyByte are heavily connected sites, they are actually very different in terms of needs and configuration.
CopyByte is more representative of the “typical” website. Though it’s hosted on my VPS, it basically functions like a site on a shared server. It has very few complicated elements and relies on almost nothing from outside of the server.
This made moving CopyByte to HTTPS relatively straightforward. I purchased an SSL certificate from NameCheap, a well-known SSL certificate reseller and I applied it to my server using my control panel. From there, I simply used the WordPress SSL plugin to handle the redirect and, more or less, I was done. The process, including testing, took less than 20 minutes.
Plagiarism Today, however, was much more complex.
Plagiarism Today is a much-higher traffic site and it uses a content delivery network, namely Distil (previous coverage). This means that, if you’re in New York, you access this site from a different endpoint (server) than someone in Paris. Since my personal server doesn’t handle the connections, it just feeds Distil’s endpoints, installing the certificate on it would do no good.
Fortunately, Distil had a solution for this. They keep a multi-domain certificate and were able to register Plagiarism Today on it. This made it easy to flip the switch and turn Plagiarism Today into an HTTPS site. But, unfortunately, that was where my struggles were just beginning.
Third Party Issues
Like a lot of sites, Plagiarism Today uses a variety of third-party apps and services to help provide a additional features. Unfortunately, when a site is HTTPS only, if those services aren’t HTTPS-ready, they will break.
The worst two culprits were the comments, which previously were powered by Livefyre, and the Copyright 2.0 Show chatroom. Neither the comments nor the chatroom were available in a secure manner so they broke when the site went to httpss. I simply disabled Livefyre, returning to native WordPress commenting and installed a new IRC-based chatroom that works with HTTPS-compliant sites.
However, the problem that surprised me was Google’s custom search function, which I have used for years to help users find content on the domain, also broke when the site went HTTPS. However, updating the code to the latest version fixed that issue, and provided an opportunity to better style it for the site.
Also, one widget provided by the Copyright Alliance had to be temporarily removed (it will likely be restored tonight as they say they have addressed the issue), and I also had to purge a handful of references to an old Amazon Cloudfront server I had used years ago, which caused images on some older posts to break.
All in all, this process was much more complex and, most likely, still not complete. I fully expect to spot additional issues as I continue to work on the site. However, the major ones appear to be cleaned up, even if it took several days of off-and-on work/testing.
Additional Tips and Recommendations
Before I wrap up, here are a few additional tips and thoughts for anyone looking to move their site to httpss:
- Extended Validation: There are two types of SSL certificates, Extended Validation (EV) and Domain Validation (DV). EV certificates cost significantly more and take much longer to issue as the issuer must verify the company/person behind the domain. DV only requires the domain itself be validated and cost only a few dollars per year and take just minutes to issue. DV is adequate for providing basic httpss functionality though EV does have the added benefit of the green address bar with the company name.
- Shared Hosting: If you have a shared hosting account or otherwise share an IP address with other sites, you’ll need to have Server Name Indication (SNI) enabled in order to make your site HTTPS, which most do. The drawback of SNI is that the browser must also support it and, though most modern browsers do, Internet Explorer for Windows XP (including version 8) does not.
- Securing Admin: Even if you don’t want to go through the trouble of making your entire site HTTPS, it makes sense to go ahead and secure your login page. You can just edit your wp-config file. You don’t even need to buy a certificate. Though your site won’t show up as having a valid certificate, that’s fine because it’s just for you and the encryption is still working.
If you are looking to make the full switch, here are a few things you should probably do before getting started:
- Check Your Host: Make sure your host can and will support your move to HTTPS. most hosts can without any problem, but it’s worth looking into, especially if you are on inexpensive hosting.
- Take Inventory: Check every third-party service you use, including social media icon, analytics, image hosts, toolbars, etc. to ensure that they can work with a secure version of your site.
- Test, Test and Test: Test your site in HTTPS. You can do this with a self-generated certificate, meaning no cost. Though the certificate won’t register as valid, it will let you see how well your site works in HTTPS before buying the certificate and opening it up to others.
Indeed, the last step is where I fell down the most. Unexpected problems and widgets I plain forgot about wreaked havoc on the site for a time. However, with nearly ten years of history, it shouldn’t come as a surprise that there are outdated components to the site that needed to be cleaned up.
Bottom Line
Is SSL/HTTPS perfect? Absolutely not. There are ways to break the protection SSL/TLS provides and switching your site to secure doesn’t prevent anyone from knowing what domain they are visiting since certificates are issued on a domain level. However, the actual URL visited will remain hidden.
Still, httpss makes the Web more secure and more private. It’s something that most webmaster can trivially do and it not only help protects your visitors, but it can help protect you. After all, you, more than anyone, log in and exchange information over your site. It makes sense to know that you have a secure connection when doing so.
So the move to httpss makes sense for me and probably for many others. Google is providing an added incentive, but the main reasons having nothing to do with search engine rankings.
Here’s to a more secure Internet!
Want to Reuse or Republish this Content?
If you want to feature this article in your site, classroom or elsewhere, just let us know! We usually grant permission within 24 hours.
